Microsoft-owned LinkedIn says a recent report about personal information of some 700 million users of its members being put up for sale is due to scraping of the careers social networking site, and not a new data breach.
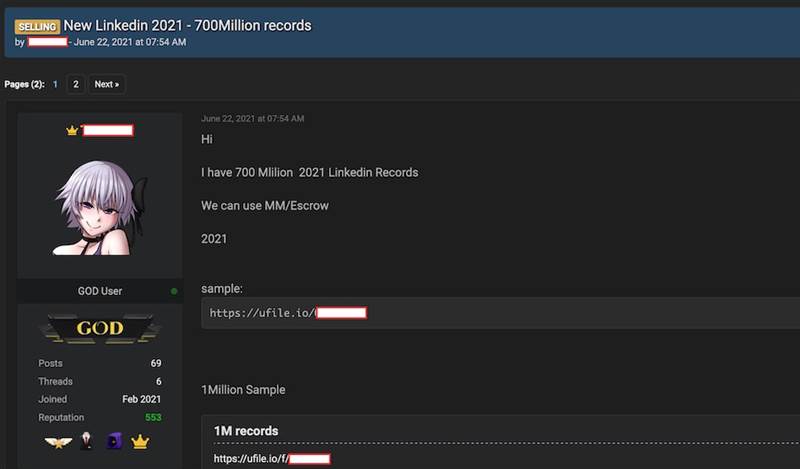
The claims of a data leak were made by Restore Privacy founder Sven Taylor, who said that a hacker had posted a sample on an unnamed internet forum with information on 1 million LinkedIn users.
Taylor said the hacker's database contains information on 700 million LinkedIn members, which is close to the full amount of users that have registered on the website.
Priced at US$5000 for the full 700 million record dataset, Taylor said the data appears to be updated with samples from 2020 to 2021.
Taylor contacted the threat actor via Telegram, and was told the data had been obtained via the LinkedIn application programming interface.
After investigating the report, LinkedIn said the data trove isn't from a breach and that no private member data was exposed.
"Our initial investigation has found that this data was scraped from LinkedIn and other various websites and includes the same data reported earlier this year in our April 2021 scraping update," LinkedIn said.
In April this year, LinkedIn said it had investigated an alleged set of data for sale, and determined the information in it had been aggregated from a number of different websites and companies.
The operator of the haveibeenpwned data leak lookup and alert website, Troy Hunt, also believed the information had been scraped from LinkedIn.
This looks like a continuation of the story earlier this year which wasn’t a breach, rather it was scraped. Newsworthy, but big difference https://t.co/OKCpECbePA
— Troy Hunt (@troyhunt) June 29, 2021
LinkedIn states that any misuse of members' data such as scraping is against its terms of service and that it will hold anyone who does so accountable.
In 2012, LinkedIn suffered a data breach of 164 million email addresses and passwords.
Cyber attackers will find the easiest way to steal data
Tim Mackey, Principal Security Strategist, Synopsys shared that from a user perspective, this breach is no different between a data breach where company servers were hacked and someone misusing an API to obtain their data.
“Data loss is data loss, and attackers will find the simplest way to obtain the data they need to fund their operations.
“As successful attacks on infrastructure become more difficult to execute, attackers will naturally shift their focus to abusing legitimate access methods like APIs provided by businesses to access data. Where legitimate users care about terms of service, criminals won’t. This is an important detail for anyone exposing an API on the internet – it’s only a matter of time before your APIs are discovered and abused. So the key question then becomes – how quickly can you detect abnormal usage and take corrective action? The more powerful your API, the more attractive it will be to criminals.”
Additional reporting by iTNews Asia Team






.jpg&h=271&w=480&c=1&s=1)